Managing Users and Groups
Introduction to Users and Groups
While users can be either people (meaning accounts tied to physical users) or accounts which exist for specific applications to use, groups are logical expressions of organization, tying users together for a common purpose. Users within a group share the same permissions to read, write, or execute files owned by that group.
Each user is associated with a unique numerical identification number called a user ID (UID). Likewise, each group is associated with a group ID (GID). A user who creates a file is also the owner and group owner of that file. The file is assigned separate read, write, and execute permissions for the owner, the group, and everyone else. The file owner can be changed only by root, and access permissions can be changed by both the root user and file owner.
Additionally, Fedora supports access control lists (ACLs) for files and directories which allow permissions for specific users outside of the owner to be set. For more information about this feature, see the Access Control Lists chapter of the Red Hat Enterprise Linux 7 System Administrators Guide.
User Private Groups
Fedora uses a user private group (UPG) scheme, which makes UNIX groups easier to manage. A user private group is created whenever a new user is added to the system. It has the same name as the user for which it was created and that user is the only member of the user private group.
User private groups make it safe to set default permissions for a newly created file or directory, allowing both the user and the group of that user to make modifications to the file or directory.
The setting which determines what permissions are applied to a newly created file or directory is called a umask and is configured in the /etc/bashrc file. Traditionally on UNIX-based systems, the umask is set to 022, which allows only the user who created the file or directory to make modifications. Under this scheme, all other users, including members of the creator’s group, are not allowed to make any modifications. However, under the UPG scheme, this “group protection” is not necessary since every user has their own private group.
A list of all groups is stored in the /etc/group configuration file.
Shadow Passwords
In environments with multiple users, it is very important to use shadow passwords provided by the shadow-utils package to enhance the security of system authentication files. For this reason, the installation program enables shadow passwords by default.
The following is a list of the advantages shadow passwords have over the traditional way of storing passwords on UNIX-based systems:
-
Shadow passwords improve system security by moving encrypted password hashes from the world-readable
/etc/passwdfile to/etc/shadow, which is readable only by therootuser. -
Shadow passwords store information about password aging.
-
Shadow passwords allow the
/etc/login.defsfile to enforce security policies.
Most utilities provided by the shadow-utils package work properly whether or not shadow passwords are enabled. However, since password aging information is stored exclusively in the /etc/shadow file, some utilities and commands do not work without first enabling shadow passwords:
-
The chage utility for setting password-aging parameters. For details, see the Password Security section in the Red Hat Enterprise Linux 7 Security Guide.
-
The gpasswd utility for administrating the
/etc/groupfile. -
The usermod command with the
-e, --expiredateor-f, --inactiveoption. -
The useradd command with the
-e, --expiredateor-f, --inactiveoption.
Managing Users in a Graphical Environment
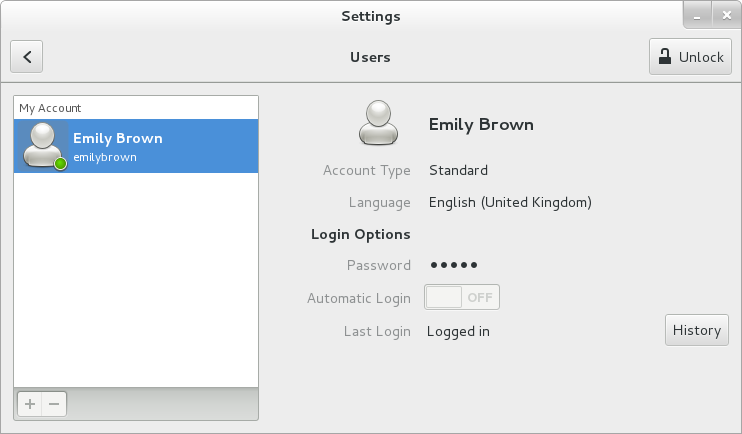
The Users utility allows you to view, modify, add, and delete local users in the graphical user interface.
Using the Users Settings Tool
Press the Super key to enter the Activities Overview, type Users and then press Enter. The Users settings tool appears. The Super key appears in a variety of guises, depending on the keyboard and other hardware, but often as either the Windows or Command key, and typically to the left of the Spacebar.
To make changes to the user accounts, first select the Unlock button and authenticate yourself as indicated by the dialog box that appears. Note that unless you have superuser privileges, the application will prompt you to authenticate as root. To add and remove users, select the + and - button respectively. To add a user to the administrative group wheel, change the Account Type from Standard to Administrator. To edit a user’s language setting, select the language and a drop-down menu appears.
The commandline for call this Gui is : [user@domain ~]$ kcmshell5 user_manager When a new user is created, the account is disabled until a password is set. The Add User menu contains the options to set a password by the administrator immediately, or to allow the user to choose a password at the first login.
Using Command Line Tools
Apart from the Users settings tool described in Managing Users in a Graphical Environment, which is designed for basic managing of users, you can use command line tools for managing users and groups that are listed in Command line utilities for managing users and groups.
| Utilities | Description |
|---|---|
id |
Displays user and group IDs. |
useradd, usermod, userdel |
Standard utilities for adding, modifying, and deleting user accounts. |
groupadd, groupmod, groupdel |
Standard utilities for adding, modifying, and deleting groups. |
gpasswd |
Standard utility for administering the |
pwck, grpck |
Utilities that can be used for verification of the password, group, and associated shadow files. |
pwconv, pwunconv |
Utilities that can be used for the conversion of passwords to shadow passwords, or back from shadow passwords to standard passwords. |
grpconv, grpunconv |
Similar to the previous, these utilities can be used for conversion of shadowed information for group accounts. |
Adding a New User
To add a new user to the system, type the following at a shell prompt as root:
useradd options username
…where options are command-line options as described in Common useradd command-line options.
By default, the useradd command creates a locked user account. To unlock the account, run the following command as root to assign a password:
passwd username
Optionally, you can set a password aging policy. See Enabling Password Aging for information on how to enable password aging.
| Option | Description |
|---|---|
|
comment can be replaced with any string. This option is generally used to specify the full name of a user. |
|
Home directory to be used instead of default |
|
Date for the account to be disabled in the format YYYY-MM-DD. |
|
Number of days after the password expires until the account is disabled. If |
|
Group name or group number for the user’s default (primary) group. The group must exist prior to being specified here. |
|
List of additional (supplementary, other than default) group names or group numbers, separated by commas, of which the user is a member. The groups must exist prior to being specified here. |
|
Create the home directory if it does not exist. |
|
Do not create the home directory. |
|
Do not create a user private group for the user. |
|
The password encrypted with crypt. |
|
Create a system account with a UID less than 1000 and without a home directory. |
|
User’s login shell, which defaults to /bin/bash. |
|
User ID for the user, which must be unique and greater than 999. |
The command-line options associated with the usermod command are essentially the same. Note that if you want to add a user to another supplementary group, you need to use the -a, --append option with the -G option. Otherwise the list of supplementary groups for the user will be overwritten by those specified with the usermod -G command.
The following steps illustrate what happens if the command useradd juan is issued on a system that has shadow passwords enabled:
-
A new line for
juanis created in/etc/passwd:juan:x:1001:1001::/home/juan:/bin/bash
The line has the following characteristics:
-
It begins with the user name
juan. -
There is an
xfor the password field indicating that the system is using shadow passwords. -
A UID greater than 999 is created. Under Fedora, UIDs below 1000 are reserved for system use and should not be assigned to users.
-
A GID greater than 999 is created. Under Fedora, GIDs below 1000 are reserved for system use and should not be assigned to users.
-
The optional GECOS information is left blank. The GECOS field can be used to provide additional information about the user, such as their full name or phone number.
-
The home directory for
juanis set to/home/juan/. -
The default shell is set to /bin/bash.
-
-
A new line for
juanis created in/etc/shadow:juan:!!:14798:0:99999:7:::
The line has the following characteristics:
-
It begins with the username
juan. -
Two exclamation marks (
!!) appear in the password field of the/etc/shadowfile, which locks the account.NoteIf an encrypted password is passed using the
-pflag, it is placed in the/etc/shadowfile on the new line for the user. -
The password is set to never expire.
-
-
A new line for a group named
juanis created in/etc/group:juan:x:1001:
A group with the same name as a user is called a user private group. For more information on user private groups, see User Private Groups.
The line created in
/etc/grouphas the following characteristics:-
It begins with the group name
juan. -
An
xappears in the password field indicating that the system is using shadow group passwords. -
The GID matches the one listed for
juan's primary group in/etc/passwd.
-
-
A new line for a group named
juanis created in/etc/gshadow:juan:!::
The line has the following characteristics:
-
It begins with the group name
juan. -
An exclamation mark (
!) appears in the password field of the/etc/gshadowfile, which locks the group. -
All other fields are blank.
-
-
A directory for user
juanis created in the/home/directory:~]# ls -ld /home/juan drwx------. 4 juan juan 4096 Mar 3 18:23 /home/juan
This directory is owned by user
juanand groupjuan. It has read, write, and execute privileges only for the userjuan. All other permissions are denied. -
The files within the
/etc/skel/directory (which contain default user settings) are copied into the new/home/juan/directory. The contents of/etc/skel/may vary depending on installed applications:~]# ls -la /home/juan total 24 drwx------. 4 juan juan 4096 Mar 3 18:23 . drwxr-xr-x. 5 root root 4096 Mar 3 18:23 .. -rw-r--r--. 1 juan juan 18 Jul 09 08:43 .bash_logout -rw-r--r--. 1 juan juan 176 Jul 09 08:43 .bash_profile -rw-r--r--. 1 juan juan 124 Jul 09 08:43 .bashrc drwxr-xr-x. 4 juan juan 4096 Jul 09 08:43 .mozilla
At this point, a locked account called juan exists on the system. To activate it, the administrator must next assign a password to the account using the passwd command and, optionally, set password aging guidelines.
Adding a New Group
To add a new group to the system, type the following at a shell prompt as root:
groupadd options group_name
…where options are command-line options as described in Common groupadd command-line options.
| Option | Description |
|---|---|
|
When used with |
|
Group ID for the group, which must be unique and greater than 999. |
|
Override |
|
Allows creating groups with duplicate GID. |
|
Use this encrypted password for the new group. |
|
Create a system group with a GID less than 1000. |
Enabling Password Aging
For security reasons, it is advisable to require users to change their passwords periodically. This can be done by using the chage command.
|
Shadow passwords must be enabled to use chage
Shadow passwords must be enabled to use the chage command. For more information, see Shadow Passwords. |
To configure password expiration for a user from a shell prompt, run the following command as root:
chage options username
…where options are command line options as described in chage command line options. When the chage command is followed directly by a username (that is, when no command line options are specified), it displays the specified users current password aging values and allows you to change these values interactively.
| Option | Description |
|---|---|
|
Specifies the number of days since January 1, 1970 the password was changed. |
|
Specifies the date on which the account is locked, in the format YYYY-MM-DD. Instead of the date, the number of days since January 1, 1970 can also be used. |
|
Specifies the number of inactive days after the password expiration before locking the account. If the value is |
|
Lists current account aging settings. |
|
Specify the minimum number of days after which the user must change passwords. If the value is |
|
Specify the maximum number of days for which the password is valid. When the number of days specified by this option plus the number of days specified with the |
|
Specifies the number of days before the password expiration date to warn the user. |
You can configure a password to expire the first time a user logs in. This forces users to change passwords immediately.
-
Set up an initial password. There are two common approaches to this step: you can either assign a default password, or you can use a null password.
To assign a default password, type the following at a shell prompt as
root:passwd usernameTo assign a null password instead, use the following command:
passwd
-dusernameAvoid using null passwords whenever possibleUsing a null password, while convenient, is a highly insecure practice, as any third party can log in first and access the system using the insecure username. Always make sure that the user is ready to log in before unlocking an account with a null password.
-
Force immediate password expiration by running the following command as
root:chage
-d0usernameThis command sets the value for the date the password was last changed to the epoch (January 1, 1970). This value forces immediate password expiration no matter what password aging policy, if any, is in place.
Upon the initial log in, the user is now prompted for a new password.
Enabling Automatic Logouts
Especially when the user is logged in as root, an unattended login session may pose a significant security risk. To reduce this risk, you can configure the system to automatically log out idle users after a fixed period of time:
-
Make sure the screen package is installed. You can do so by running the following command as
root:dnf
installscreenFor more information on how to install packages in Fedora, refer to Installing Packages.
-
As
root, add the following line at the beginning of the/etc/profilefile to make sure the processing of this file cannot be interrupted:trap "" 1 2 3 15
-
Add the following lines at the end of the
/etc/profilefile to start a screen session each time a user logs in to a virtual console or remotely:SCREENEXEC="screen" if [ -w $(tty) ]; then trap "exec $SCREENEXEC" 1 2 3 15 echo -n 'Starting session in 10 seconds' sleep 10 exec $SCREENEXEC fi
Note that each time a new session starts, a message will be displayed and the user will have to wait ten seconds. To adjust the time to wait before starting a session, change the value after the sleep command.
-
Add the following lines to the
/etc/screenrcconfiguration file to close the screen session after a given period of inactivity:idle 120 quit autodetach off
This will set the time limit to 120 seconds. To adjust this limit, change the value after the
idledirective.Alternatively, you can configure the system to only lock the session by using the following lines instead:
idle 120 lockscreen autodetach off
This way, a password will be required to unlock the session.
The changes take effect the next time a user logs in to the system.
Creating Group Directories
System administrators usually like to create a group for each major project and assign people to the group when they need to access that project’s files. With this traditional scheme, file management is difficult; when someone creates a file, it is associated with the primary group to which they belong. When a single person works on multiple projects, it becomes difficult to associate the right files with the right group. However, with the UPG scheme, groups are automatically assigned to files created within a directory with the setgid bit set. The setgid bit makes managing group projects that share a common directory very simple because any files a user creates within the directory are owned by the group that owns the directory.
For example, a group of people need to work on files in the /opt/myproject/ directory. Some people are trusted to modify the contents of this directory, but not everyone.
-
As
root, create the/opt/myproject/directory by typing the following at a shell prompt:mkdir /opt/myproject -
Add the
myprojectgroup to the system:groupadd myproject -
Associate the contents of the
/opt/myproject/directory with themyprojectgroup:chown root:myproject /opt/myproject -
Allow users in the group to create files within the directory and set the setgid bit:
chmod 2775 /opt/myprojectAt this point, all members of the
myprojectgroup can create and edit files in the/opt/myproject/directory without the administrator having to change file permissions every time users write new files. To verify that the permissions have been set correctly, run the following command:~]# ls -ld /opt/myproject drwxrwsr-x. 3 root myproject 4096 Mar 3 18:31 /opt/myproject
-
Add users to the
myprojectgroup:usermod -aG myproject username
Additional Resources
For more information on how to manage users and groups on Fedora, see the resources listed below.
For information about various utilities for managing users and groups, see the following manual pages:
-
useradd(8) — The manual page for the useradd command documents how to use it to create new users. -
userdel(8) — The manual page for the userdel command documents how to use it to delete users. -
usermod(8) — The manual page for the usermod command documents how to use it to modify users. -
groupadd(8) — The manual page for the groupadd command documents how to use it to create new groups. -
groupdel(8) — The manual page for the groupdel command documents how to use it to delete groups. -
groupmod(8) — The manual page for the groupmod command documents how to use it to modify group membership. -
gpasswd(1) — The manual page for the gpasswd command documents how to manage the/etc/groupfile. -
grpck(8) — The manual page for the grpck command documents how to use it to verify the integrity of the/etc/groupfile. -
pwck(8) — The manual page for the pwck command documents how to use it to verify the integrity of the/etc/passwdand/etc/shadowfiles. -
pwconv(8) — The manual page for the pwconv, pwunconv, grpconv, and grpunconv commands documents how to convert shadowed information for passwords and groups. -
id(1) — The manual page for the id command documents how to display user and group IDs.
For information about related configuration files, see:
-
group(5) — The manual page for the/etc/groupfile documents how to use this file to define system groups. -
passwd(5) — The manual page for the/etc/passwdfile documents how to use this file to define user information. -
shadow(5) — The manual page for the/etc/shadowfile documents how to use this file to set passwords and account expiration information for the system.
Want to help? Learn how to contribute to Fedora Docs ›